Infosec Technologies China: A Smarter Way to Secure Enterprise Access, Applications, and Data

In today’s digital business landscape, data moves fast across applications, networks, cloud environments, and hybrid infrastructure. This level of connectivity helps companies move faster, serve customers better, and run operations more efficiently. But as digital connections expand, so does the need to keep every data exchange secure, controlled, and protected. That is why data security […]
Data Leaks Through AI Without You Realizing it? Why Businesses Need AI Detection and Response
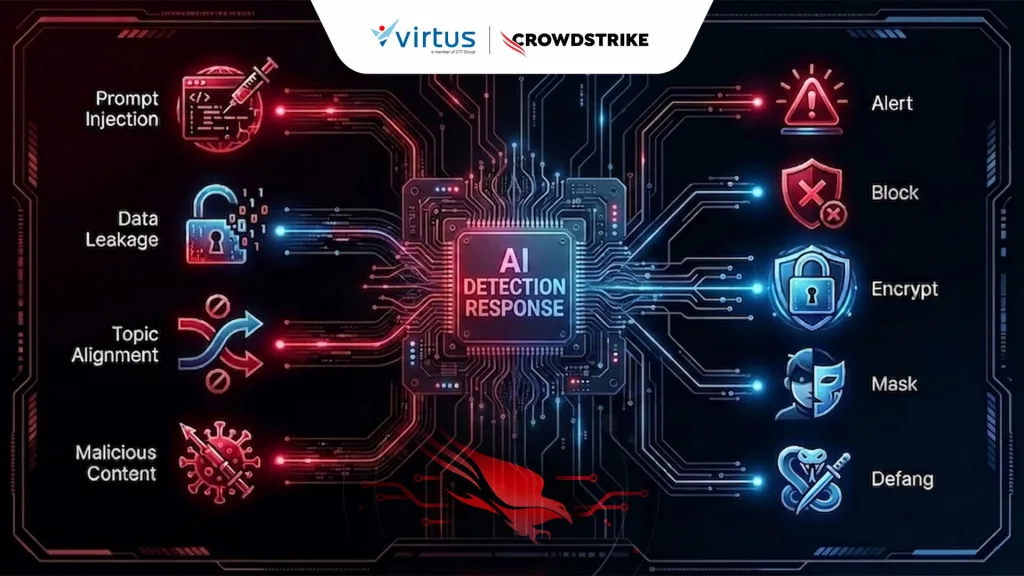
AI adoption across enterprises is accelerating rapidly. Employees now rely on various AI tools to improve productivity, from writing emails and analyzing data to assisting with coding tasks. However, behind this efficiency lies a new security risk that often goes unnoticed. Imagine an employee unintentionally uploading customer data, internal source code, or sensitive business documents […]
Too Many False Alarms? AI Security Cameras Can Cut Them by Up to 90%

Enterprise security systems today face far greater challenges than in previous years. Organizations no longer need surveillance systems that simply record footage for post-incident investigations, but solutions capable of detecting potential threats in real time before risks escalate further. Unfortunately, many businesses still rely on traditional passive surveillance systems. Cameras continuously record activity, while security […]
Too Many Alerts, Too Little Time? See How AI-Powered SecOps Helps SOC Move Faster

Cyber threats are evolving faster than ever, yet many Security Operations Center (SOC) teams still rely on manual processes. Every day, analysts deal with thousands of alerts, slow investigations, and repetitive event reviews just to identify which threats truly matter. This creates a dangerous gap. Attackers are already leveraging automation and AI, while many organizations […]
Is Your Legacy Network a Security Risk? Upgrade to Arista Cognitive Campus Switches Now

The complexity of modern networks has grown significantly with the rise of connected devices, real-time applications, and increasing connectivity demands. Many organizations are realizing that traditional networking approaches can no longer provide the visibility, security, and performance required to support today’s dynamic business operations. An adaptive solution is needed—one that minimizes downtime, eliminates blind spots, […]
What is Digital Employee Experience (DEX) and Why It Matters in Digital Workplaces?

As organizations accelerate the adoption of hybrid work, cloud, and digital workspaces, the way employees interact with technology is evolving rapidly. However, this transformation also introduces new challenges, digital experiences that are inconsistent, slow, and often disruptive to productivity. Across industries such as banking, government, manufacturing, and telecommunications, these issues are no longer just technical […]
From Concept to Implementation: Understanding Next-Generation Data Center Network Architecture

Today, the role of the data center has undergone a major transformation. It is no longer just a data storage facility but has evolved into a central operational hub that powers nearly every aspect of modern business. The surge in traffic driven by AI, cloud computing, and IoT has significantly increased the demand for more […]
Slow Network? Here’s the Right Enterprise Switch for a More Stable Network

As digital transformation accelerates across industries, from campuses and hotels to office buildings, network infrastructure is no longer just a supporting component. It has become the backbone of business operations. Even a minor disruption can directly impact productivity, user experience, and ultimately revenue. This is where an enterprise switch plays a critical role: ensuring the […]
Is Application Management Becoming More Complex? Omnissa App Volumes Offers a Faster, More Cost-Efficient Approach

As organizations accelerate the adoption of VDI, cloud, and hybrid workspaces, the way applications are managed is evolving rapidly. However, many companies are still relying on outdated approaches to application management, particularly static golden images that are difficult to maintain and scale. While this method may have worked in the past, it is no longer effective in today’s modern […]
OpenShift Introduces a New Way to Build Modern Applications Faster and More Securely

In today’s fast-moving and highly competitive landscape, businesses are under constant pressure to innovate faster. IT infrastructure is no longer just a support function—it has become a critical factor in determining how quickly new ideas can be developed, deployed, and scaled. However, the reality is that many organizations, from banking to manufacturing, still operate with […]
